Momentaufnahme aktueller Cyberangriffe auf Alyne
Obwohl Alyne ein relativ kleines Unternehmen ist, sind wir überraschend vielen gezielten Phishing-Angriffen ausgesetzt. Unsere Kunden vertrauen Alyne hochsensible Daten zur Verarbeitung an, und es liegt in unserer Verantwortung, diese Daten - und das Vertrauen - gut zu hüten.
Für alle bei Alyne bedeutet das, dass wir wachsam bleiben und sicherstellen müssen, dass wir über diese Versuche informiert sind. Eine Möglichkeit, das Bewusstsein zu schärfen, besteht darin, erfolglose Phishing-Versuche öffentlich zu machen, damit andere sehen können, wie diese Angriffe aussehen und sie in Zukunft sicher vermeiden können.
Im folgenden Beitrag möchte ich einige der Versuche der letzten Monate vorstellen.
Methoden
In diesem Beitrag analysiere ich nur die Phishing-Versuche per E-Mail. Unser App-Endpunkt ist natürlich dem Internet ausgesetzt und daher vielen Angriffen ausgesetzt, aber die Sicherheitsarchitektur - insbesondere unser CDN und die minimierte Angriffsfläche - verhindern, dass diese ein Problem darstellen.
- Phishing-Links
Bei den einfachsten Versuchen wird versucht, den Benutzer dazu zu bringen, auf einen Link zu klicken, der mit mehr oder weniger Geschick maskiert ist. - Links zu Cloud-Diensten
Eine der Methoden, die mich am meisten beunruhigt, ist die Nutzung von Cloud-Diensten, die ein Unternehmen möglicherweise tatsächlich nutzt, um betrügerische E-Mails zu versenden. - Reines Social Engineering
Der klassische Social-Engineering-Ansatz besteht darin, sich als Mitglied der Organisation auszugeben, um eine Kommunikationsverbindung herzustellen und jemanden zu einer Handlung zu überreden, die einem Angreifer unwissentlich unangemessenen Zugang verschaffen könnte. - Gemeinsame Nutzung von aktuellen Dokumenten in Cloud-Diensten
Ein neuer Ansatz, bei dem Benutzer zur Zusammenarbeit an einem Dokument eines Cloud-Dienstes (z. B. OneDrive) eingeladen werden, wobei das Dokument einen Link zu einer bösartigen Quelle enthält.
Zielsetzungen
Natürlich kennen wir nicht die genauen Ziele der einzelnen Angriffe, aber da diese Angriffe meist in großem Maßstab durchgeführt werden, können wir uns eine allgemeine Vorstellung von den Beweggründen für die Initiativen machen.
- Zahlungsmittel und Zahlungsmitteläquivalente
Der einfachste Angriff ist der auf einfache Geldäquivalente. Wir haben einen Versuch unternommen, um zu sehen, wohin der Angriff führen würde. In diesem Fall gab sich der Angreifer/Betrüger als Geschäftsführer aus und versuchte, einen neuen Mitarbeiter dazu zu bringen, Google Play-Guthaben zu kaufen und die Abrufcodes per E-Mail zu senden. - Installation von Malware
Hier haben herkömmliche Angriffe ihren Ursprung - sie versuchen, bösartigen Code auf dem angegriffenen Rechner zu installieren, um sich unbefugten Zugriff auf das System zu verschaffen. Malware hat sich im Laufe der Zeit sicherlich weiterentwickelt, wobei Ransomware die am weitesten verbreitete Art speziell für diesen breiteren Angriffsansatz ist. - Informationsbetrug
Einige der Angriffe zielen eindeutig darauf ab, Informationen über das Opfer zu erlangen, um weitere Social Engineering-Maßnahmen durchzuführen. Das letztendliche Ziel kann immer noch darin bestehen, Bargeld zu erlangen, Malware zu installieren oder sich anderweitig unberechtigten Zugang zu verschaffen.
Beispiele
An dieser Stelle möchte ich auf einige der halb gezielten Angriffe eingehen, die wir in den letzten Monaten dokumentiert haben:
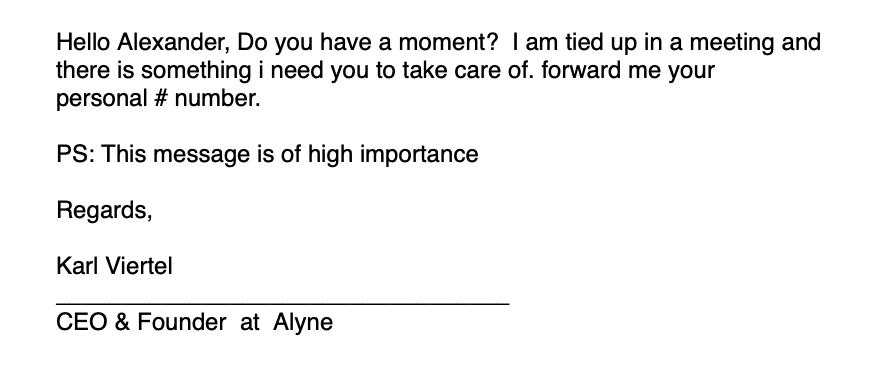
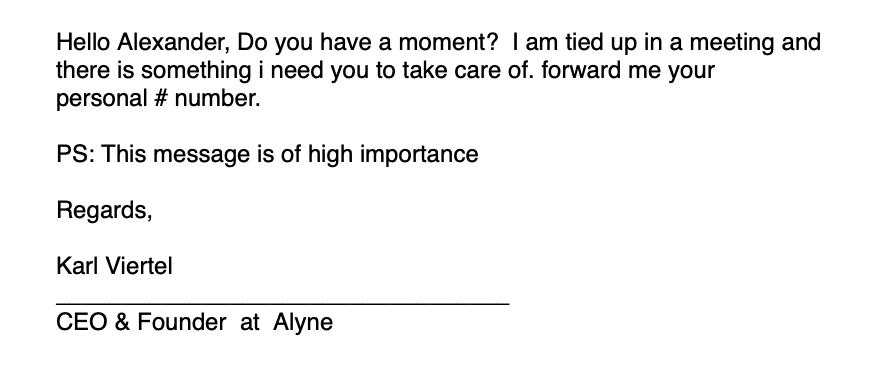
- CEO Mail Spoofing
Eines unserer neuen Teammitglieder, Alex, hat diese E-Mail erhalten - scheinbar von mir. Das Mail-Spoofing war so trivial, dass ein Klick auf den E-Mail-Absender offenbarte, dass der tatsächliche Absender mit Sicherheit nicht meine eigene E-Mail-Adresse war.
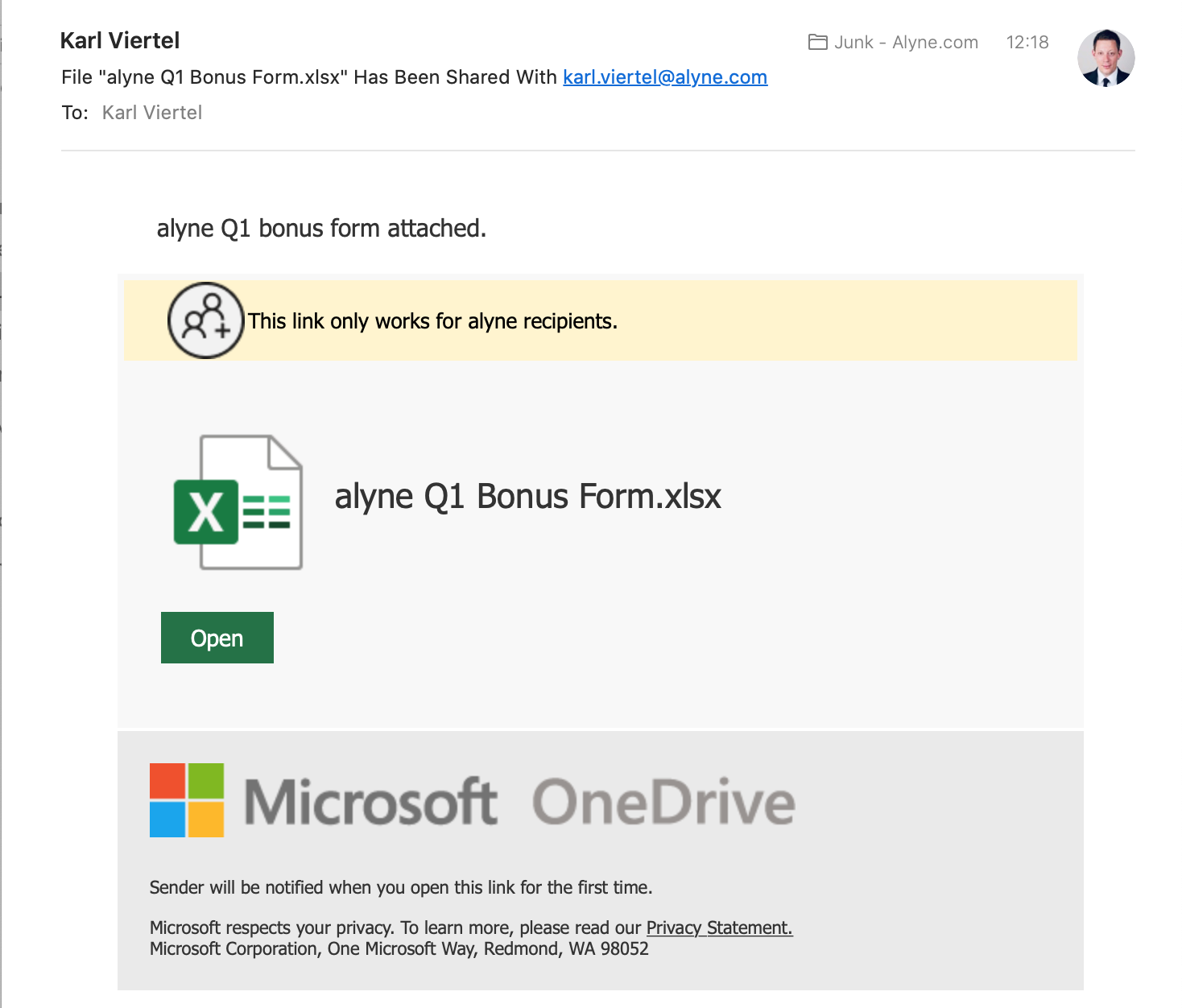
- Gefälschte Spesenabrechnungen oder Bonuszahlungsberechnungen
Interessanterweise gab es in diesem Beispiel tatsächlich eine Datei, die mit meinem Benutzer über OneDrive geteilt wurde. Obwohl niemand die Datei bei Alyne tatsächlich geöffnet hat, könnte ich mir vorstellen, dass die Datei eine Art Link oder bösartigen Inhalt enthält. Die Verlockung besteht sicherlich darin, etwas so "Aufregendes" wie Bonuszahlungen zu versenden, um die Leute dazu zu bringen, schnell zu klicken und zu schauen.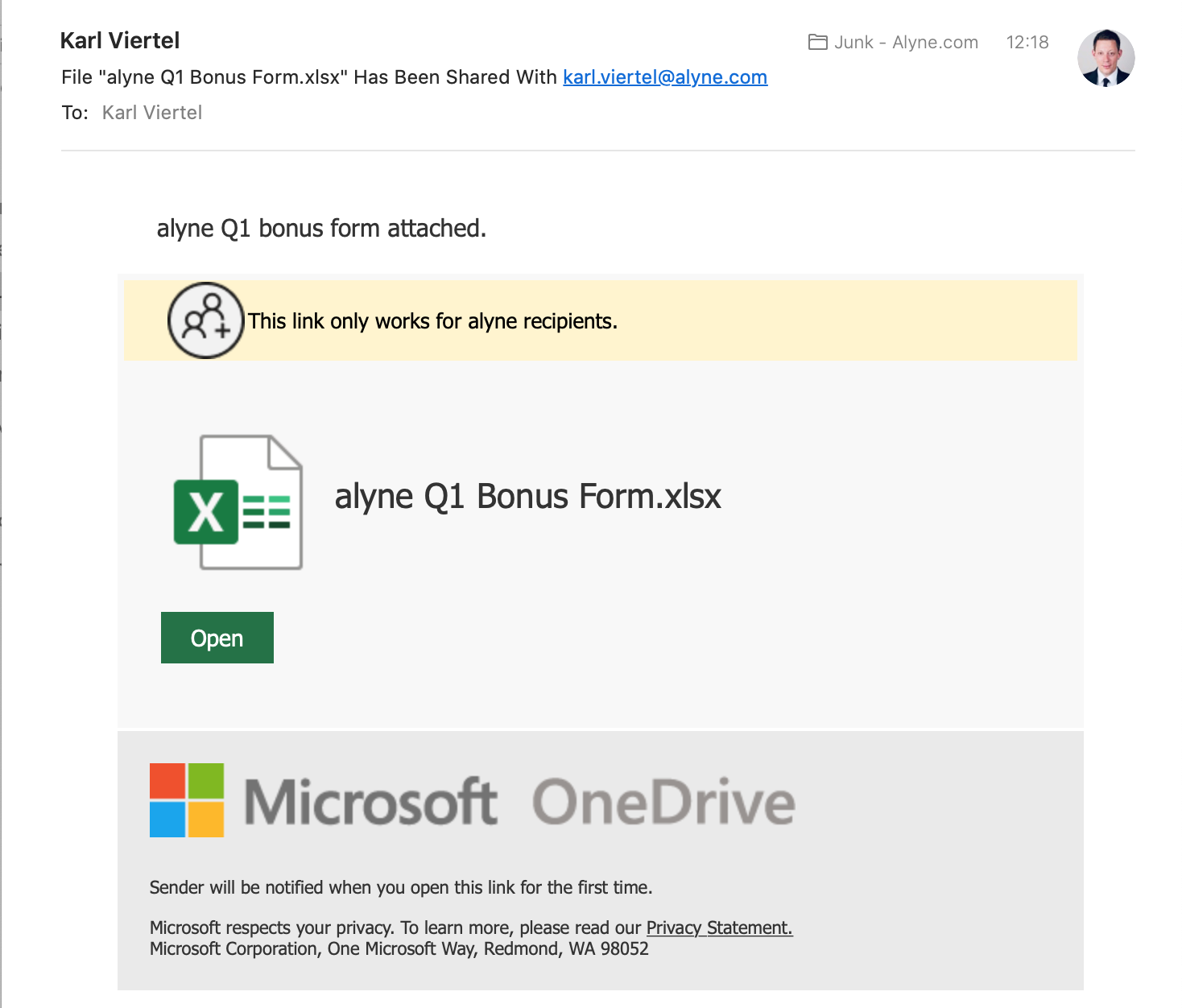
- Gefälschte Voicemail-Benachrichtigungen
Auch hier wird versucht, etwas zu senden, mit dem die Leute dringend interagieren wollen - z. B. eine verpasste Voicemail. Einige Nutzer könnten annehmen, dass es sich um ein neues System handelt, von dem sie nicht wussten, dass es eingeführt wurde, und auf den Link klicken. Die Personalisierung der Nachricht für "Alyne" ist zu beachten.

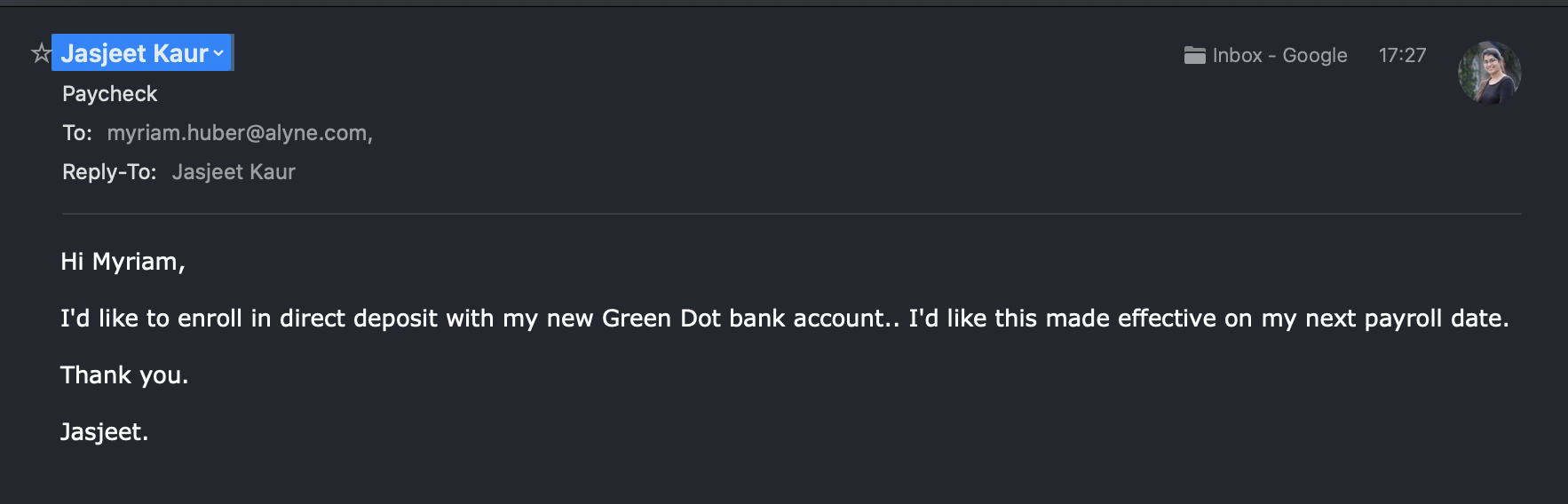
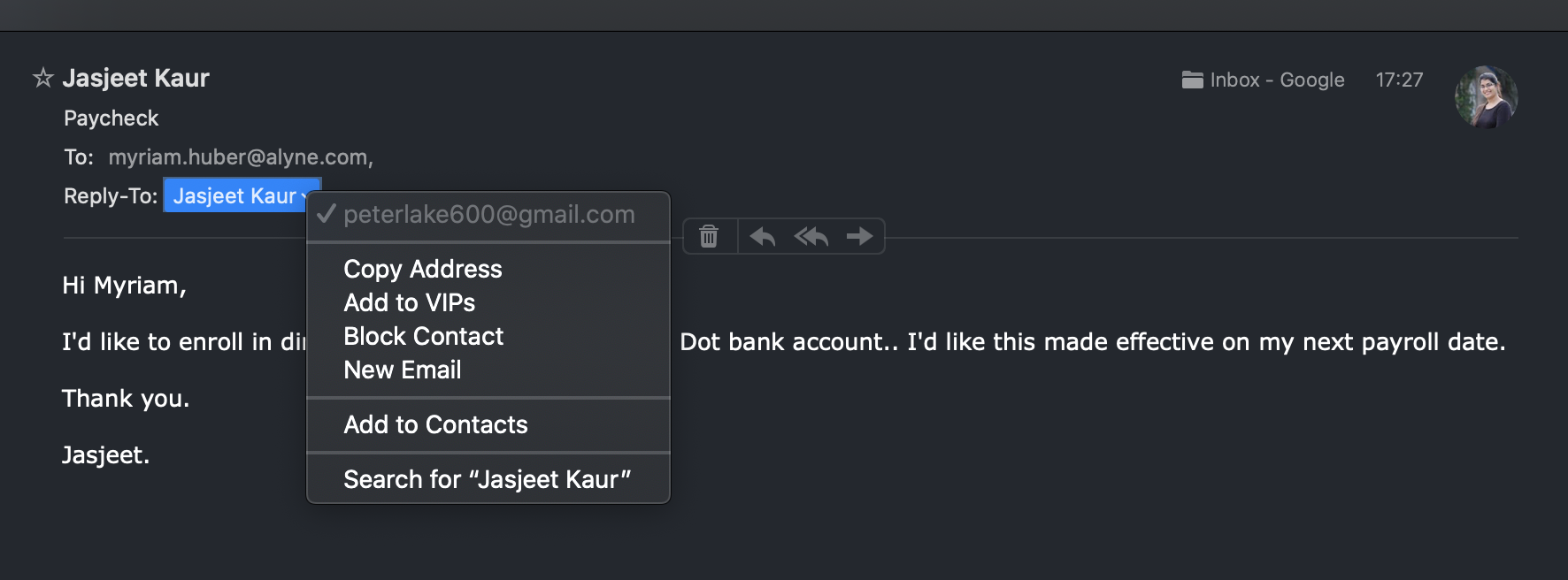
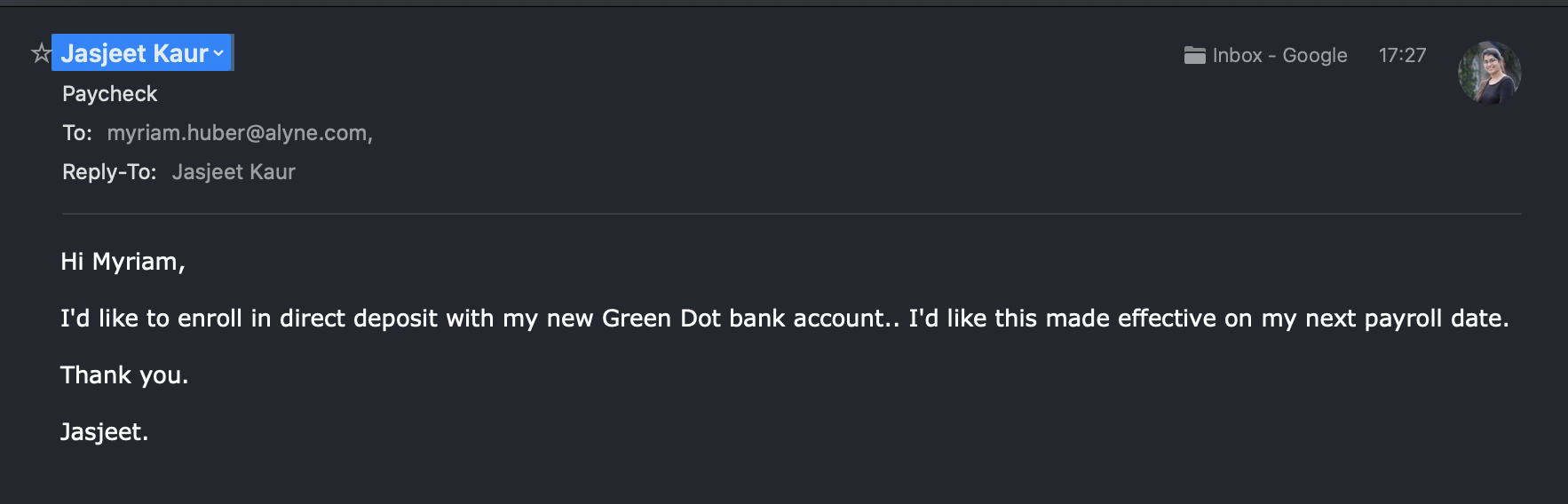
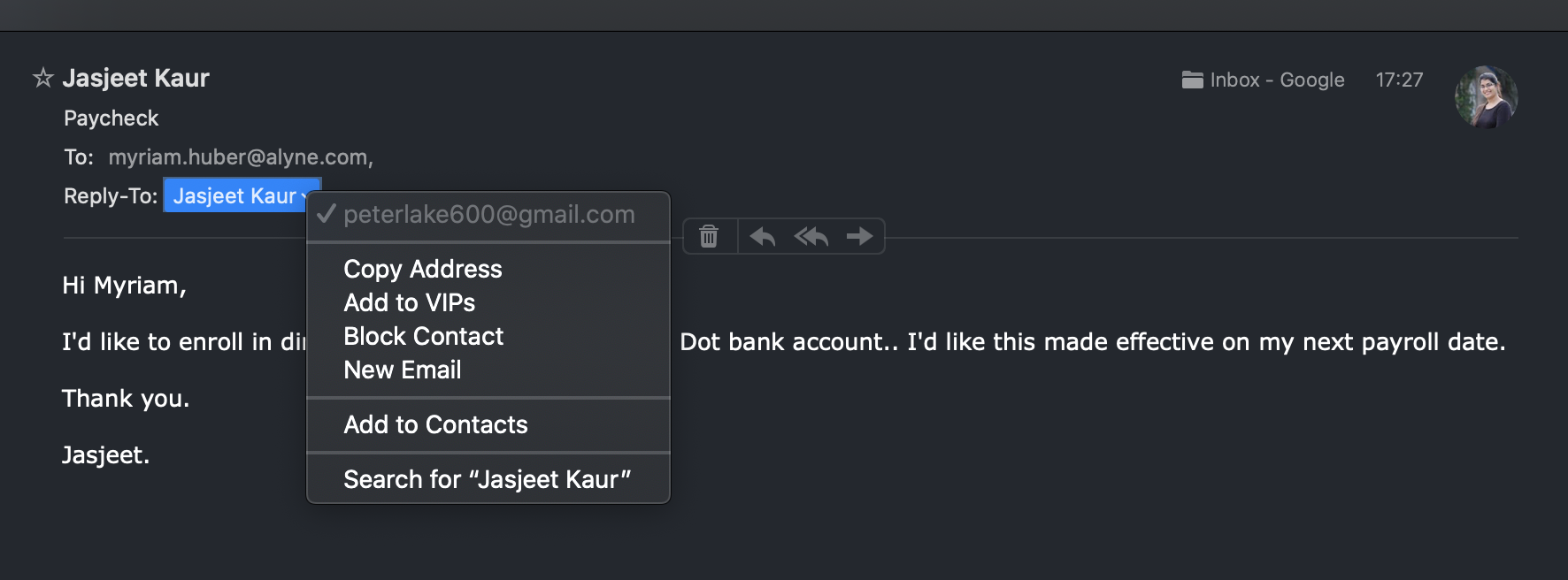
- Antrag auf Änderung der Bankverbindung
Das nächste Beispiel ist ziemlich zielgerichtet, da die Angreifer eine Mitarbeiterin und unseren Personalleiter Myri identifizierten und versuchten, das Gehaltskonto in der Personalabteilung ändern zu lassen. Myri benutzte Apple Mail und obwohl die E-Mail-Adresse eindeutig gefälscht war, zeigte Apple Mail Jasjeets Avatar an.
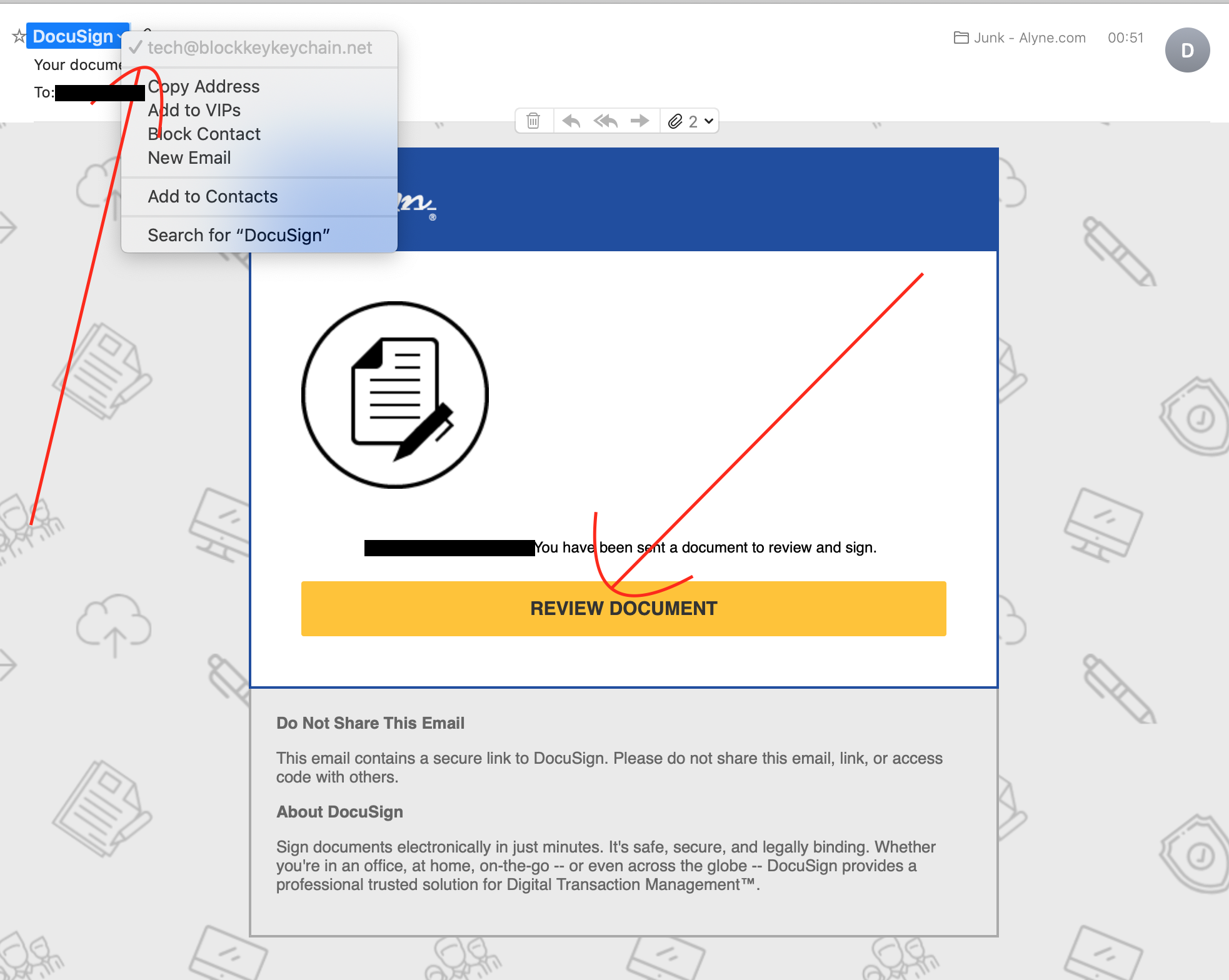
- Docusign-Betrug
Wie viele Unternehmen verwenden wir heutzutage Docusign für die Unterzeichnung unserer Dokumente. Ich erhalte eine ganze Reihe dieser Unterschriftsanfragen - manchmal von unserem Leiter der Rechtsabteilung, aber auch manchmal von unseren Kunden. Wenn Sie nicht sehr vorsichtig sind, könnte Sie diese E-Mail tatsächlich täuschen.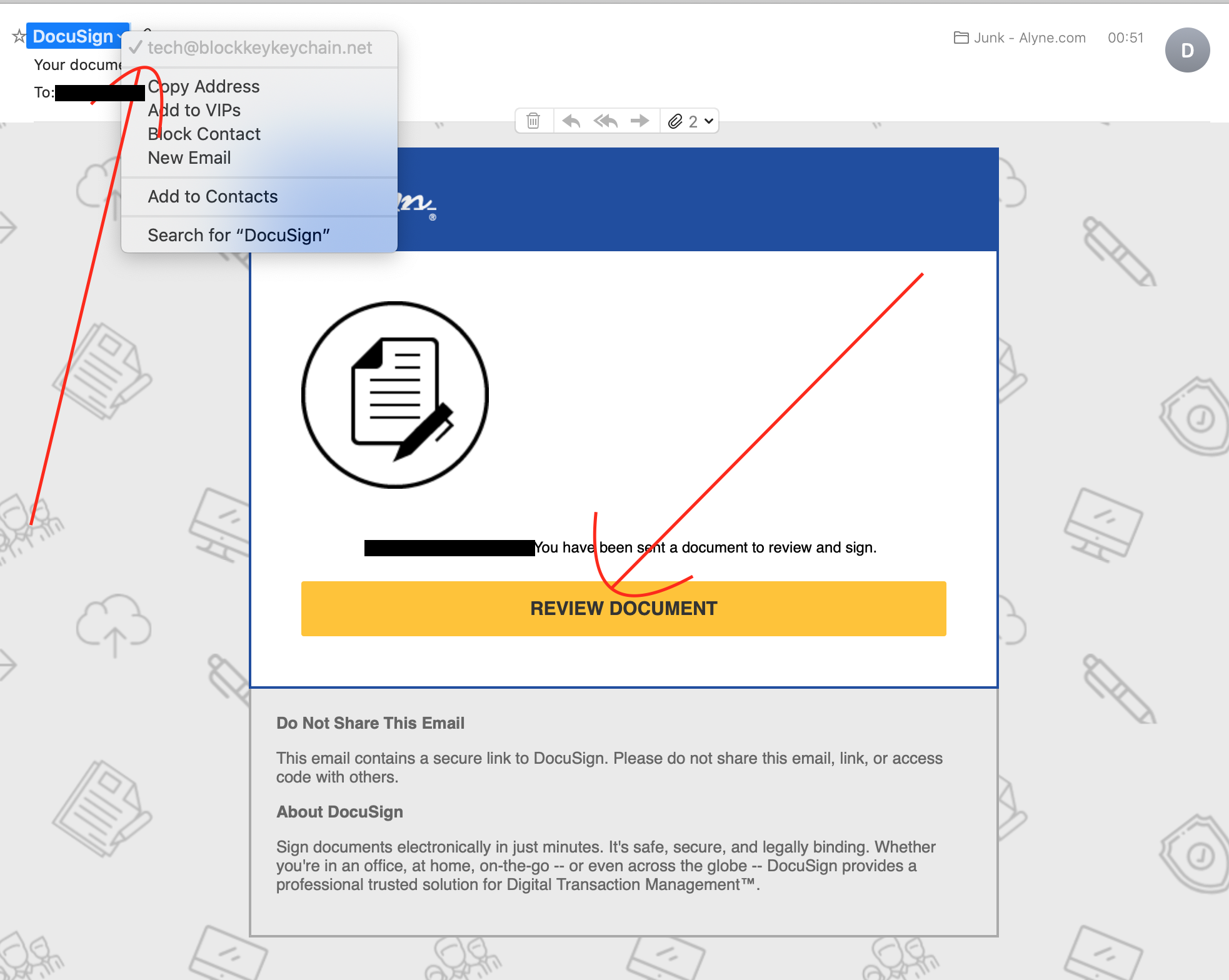
- VPN-Anmeldung
Keine sehr anspruchsvolle E-Mail, aber sehr aktuell. Da viele Menschen heute von zu Hause aus arbeiten und ein VPN nutzen, könnte der Zugang zu einem "neuen" VPN ein Grund sein, auf diesen Link zu klicken.

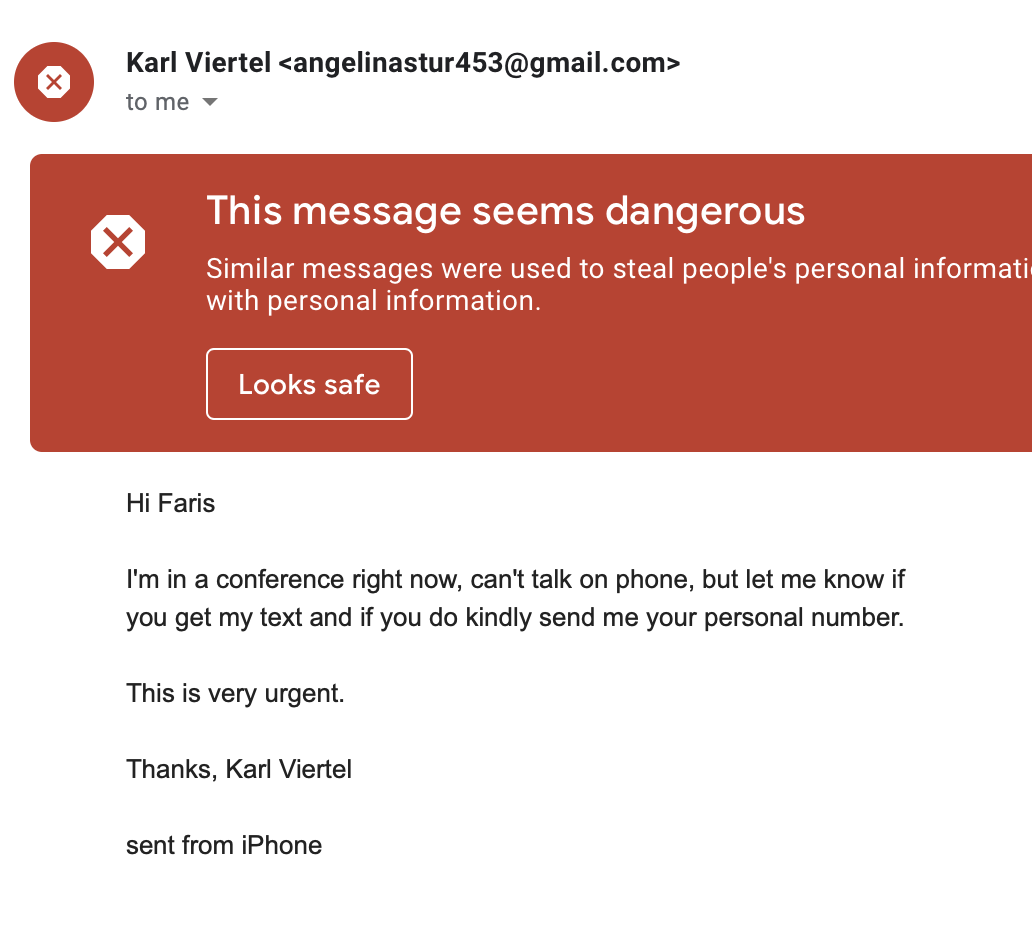
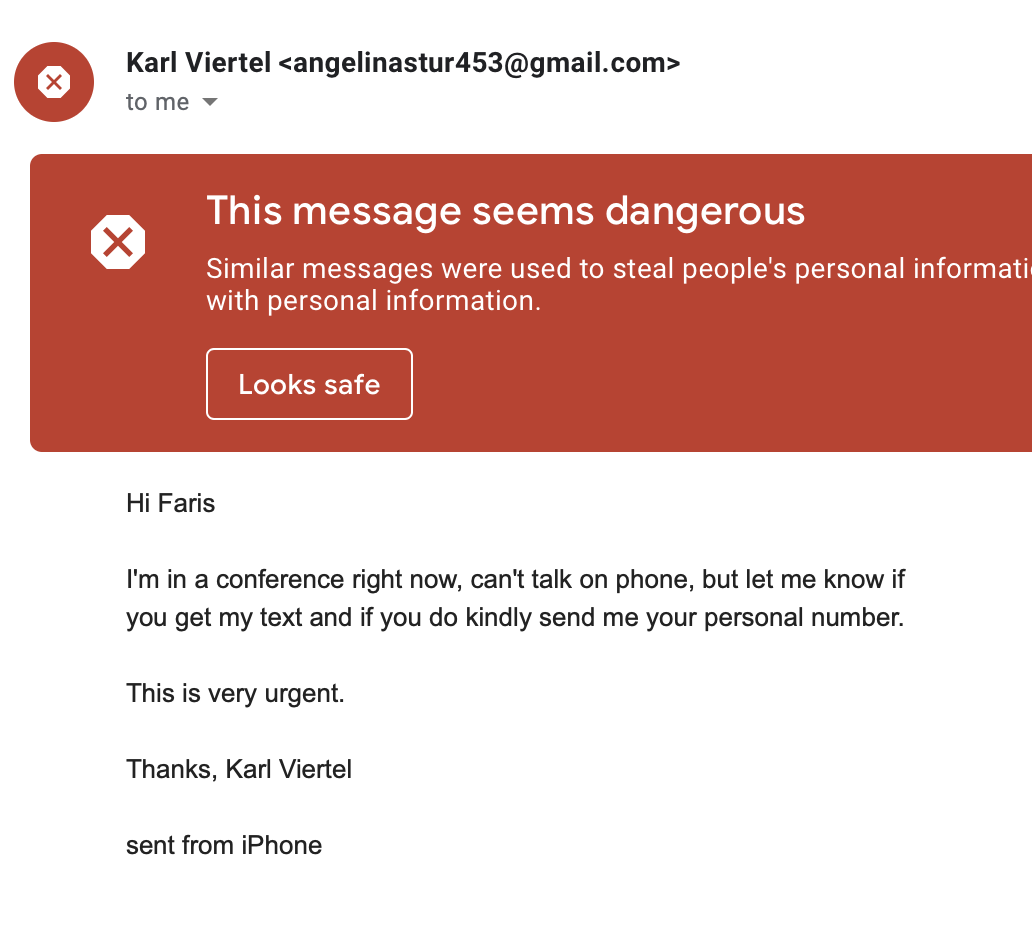
- Kontaktinformationen Phishing
Ein weiteres Beispiel, bei dem die Angreifer Faris als einen unserer Mitarbeiter identifizierten und versuchten, sich für mich auszugeben, um an Faris' Kontaktinformationen zu gelangen. Wie Sie sehen können, erhielt Faris eine ziemlich deutliche Warnung.
Bewertung
Was können wir also aus diesen Beispielen mitnehmen? Glücklicherweise waren diese Angriffe nicht sonderlich ausgeklügelt und leicht zu erkennen. Der Fokus oder die Zielgerichtetheit der Angriffe war etwas überraschend, da wir keine große Organisation sind. Ich glaube nicht, dass alle diese Informationen 100% automatisiert gesammelt werden können, sondern dass eine manuelle Konfiguration erforderlich ist, um sie auszuführen. Ein sehr klares Muster zielte auch auf neue Mitarbeiter ab, die möglicherweise nicht in der Lage sind, zwischen den tatsächlich von uns verwendeten Systemen und gefälschten Phishing-Angriffen zu unterscheiden. Im Allgemeinen sind diese Angriffe so konzipiert, dass sie in großer Zahl und mit geringer Erfolgsquote funktionieren, der Aufwand für die Konfiguration der Angriffe scheint jedoch so gering zu sein, dass er sich lohnt. Die Verwendung gängiger SaaS-Tools (Docusign, Box usw.) als Betrugsvektor zeigt, wie sich diese Angriffe weiterentwickeln. Der wohl klügste Schachzug war die Nutzung von Cloud-Dateidiensten für den Austausch von Dateien mit bösartigen Inhalten (z. B. OneDrive). Dadurch wird fast garantiert, dass die E-Mail dem Opfer zugestellt wird und Spam- und Malware-Filter unentdeckt passiert.
Abhilfemaßnahmen
Die wirksamste Maßnahme ist die Sensibilisierung des Teams. Wir thematisieren dieses Thema regelmäßig bei Besprechungen mit allen Mitarbeitern, in unseren Kommunikationskanälen und bei der Einarbeitung. Die Sensibilisierung der Mitarbeiter für die Bedrohungen durch Phishing ist entscheidend.
Bei Alyne verwenden wir Google for Work und den dazugehörigen E-Mail-Dienst. Wenn Sie die Schnittstelle des Beispiels "Änderung des Bankkontos" mit dem Beispiel "Phishing der Kontaktdaten" vergleichen, wird deutlich, dass die Verwendung der Google Mail-Schnittstelle einige erhebliche Sicherheitsvorteile bietet.
Schließlich fordern wir alle unsere Mitarbeiter auf, immer eine zweite Kanalbestätigung vorzunehmen, wenn auch nur der geringste Zweifel besteht. Unsere wichtigste Kommunikationsplattform ist Slack. Ich sage den Mitarbeitern, dass ich sie niemals per E-Mail um etwas bitten werde. Wenn ich es doch tue, bestätigen Sie es immer über einen zweiten Kanal (Telefon, Slack, persönlich).